Hunting Threat Actors with TLS Certificates
Using open source data to defend networks
Mark Parsons / @markpars0ns / mark at accessviolation.org
Introduction
Who am I
Mark Parsons
- Incident responder and Network defender
- Small time python programmer
- Occasional Threat Analyst
Who am I not
Animator - Archer
One Direction Fan Fiction???

Traditional methods of hunting
- WHOIS tracking and name server monitoring
- Passive DNS
- Malware/Implant tracking (VT, Malwr, TotalHash etc)
What else could we do that provides pivotable/trackable data
That's right TLS certificates!!!
Quick Caveat
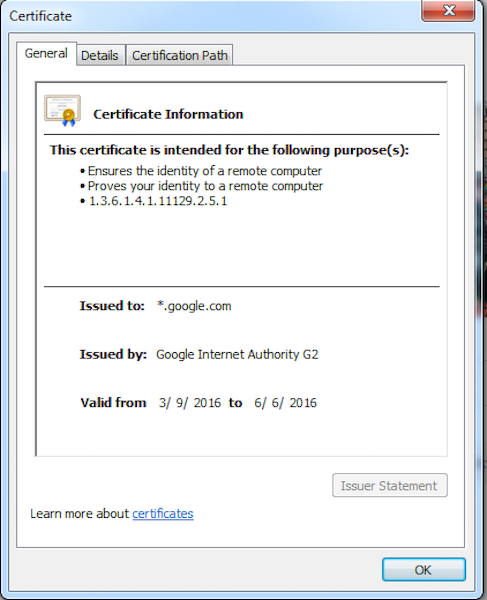
Code signing certificate != TLS certificate
Code signing
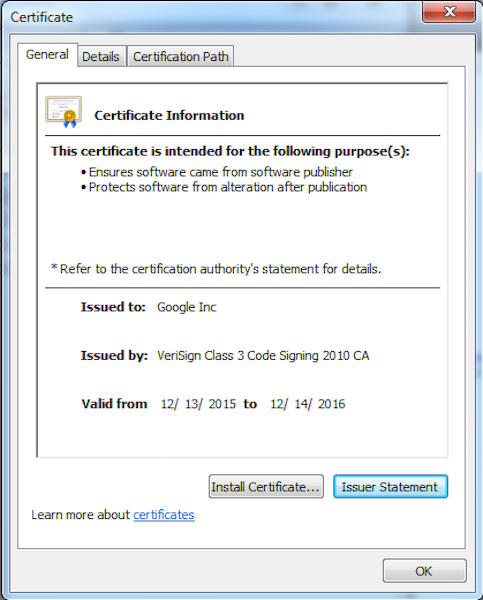
TLS certificate
TLS Hunting Basics
Tips to help you get started
Where to start
- IP to Cert
- Cert to IP
What to consider
- Look at the time frame cert was seen on an IP
- Was cert seen during malicious activity?
- Do you have malware/implant using TLS?
- How many other hosts are seen using that TLS cert?
- Expiration dates on certs
- Issuer
- Self Signed
- Free cert
- Paid cert
Network Defense
What you can do to defend your networks
IDS Monitoring - TLS fingerprints
- Suricata
- Bro
Automate tracking of TLS certs
- PassiveTotal Monitoring
- Censys.io API script
- Your own local sonar or censys.io repo
- Combo of all of these
- Put new ip addresses found into monitoring/blocks as needed
More Network defense
More Like Network Hygiene
Most of these you will have to do with your own sonar scan data or censys.io data
Look at your netblocks
- Use your ASN for a censys.io search
- Use your ASN or subnets if sonar data in elasticsearch
What to look for
- Your security appliances
- Remote access management
- HP integrated Lights Out
- Dell Remote Access Card
- Websites or services you didn't know about
Look outside your netblocks
- Look for certs for your org not inside your netblocks
- Look for certs that have email addresses from your org
- Look for certs who have your org as a Subject Alt Name
- Look for dopplegangers of your org
- Take a look at PassiveTotal keyword searching (DNS, Whois, TLS ) aka brand monitoring
So TLS certificates you say?
Where do you start?
First you need some data
You could ingest scans.io sonar SSL scans
Checkout my Scansio-Sonar-ES github repo
Or use censys.io
Or use PassiveTotal
Scans.io Sonar SSL scans
Scans performed by Rapid7
- Raw data going back to 10/30/2013
- Easily consumable
- Updated weekly
- Incremental in nature
- certs.gz - Only new sha1s and base64 raw cert seen that week
- hosts.gz - SHA1 and host for all hosts seen
- No public search interface
- Is weekly frequent enough ?
Censys.io
Maintained by the University of Michigan and University of Illinois Urbana-Champaign
- Easy to use search interface
- API Access
- Frequent Updates
- All or nothing in nature
- If there is a delta between scans old scan data is not in main search interface
- Old scan data is available in json format
PassiveTotal
- Should be the first place any analyst goes when performing any infrastructure hunting
- Merge traditional hunting with new methods
- Aggregates multiple passive DNS sources
- Provides WHOIS data
- Provides references to OpenSource reporting
- Also has TLS certificates
- So much more I am only touching the surface
If you aren't you using it
You really should try it out
You won't regret it
Disclamer: PassiveTotal provided me researcher access for data required for this presentation
Let's do some TLS hunting/pivoting
CVE-2014-1761
Remote Code Execution - Word RTF Memory Corruption Vulnerability
Awesome technet article
Yara Sigs!
TLS SHA1 Hash
Command and Control IP
Potential Command and Control Domain
Starting point

Let's do some traditional pivots
Passive DNS records for times when the TLS certs were active
Whois on any relevant domains found
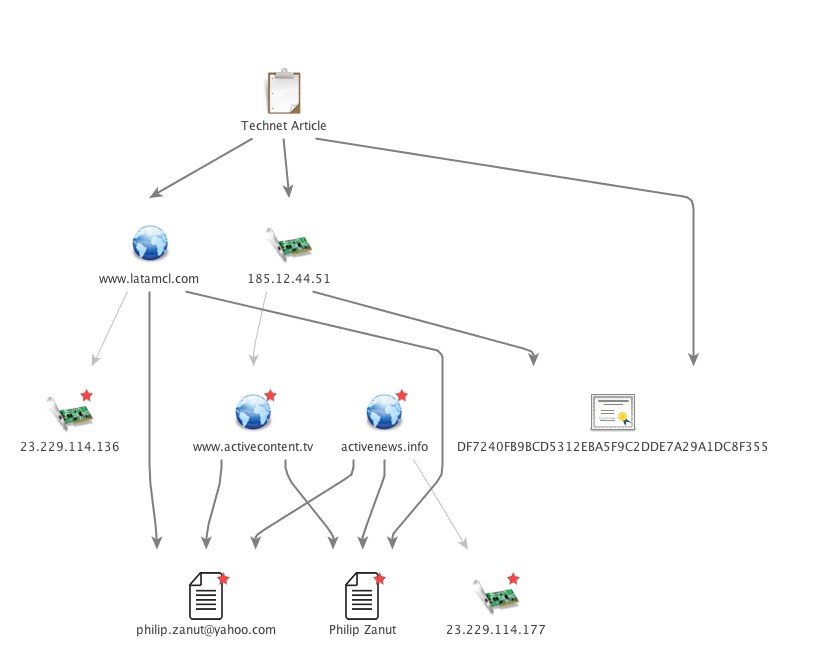
Now let's pivot on the TLS SHA1
SHA1: df7240fb9bcd5312eba5f9c2dde7a29a1dc8f355
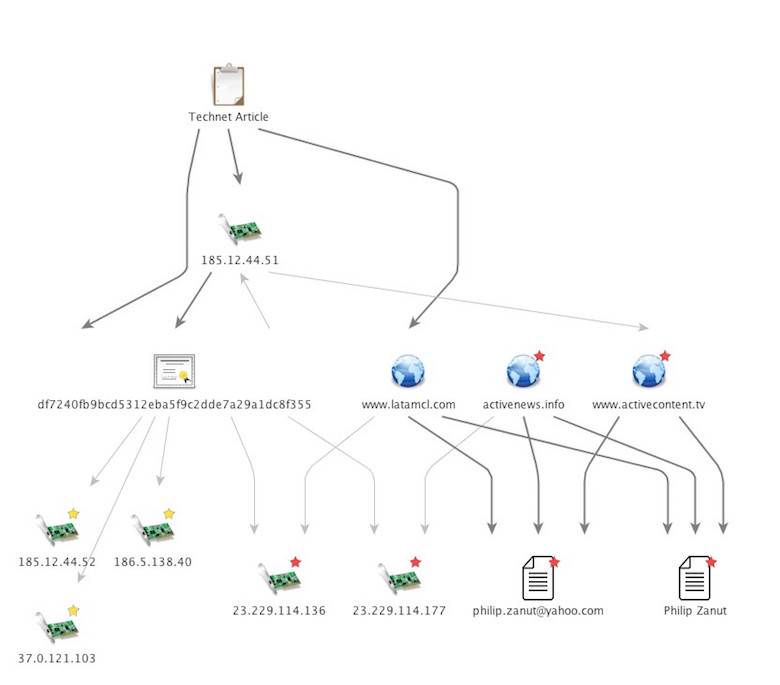
Timeframe
| IP | First Seen | Last Seen |
|---|---|---|
| 37.0.121.103 | Oct. 30, 2013 | Dec. 29, 2014 |
| 185.12.44.51 | Oct. 30, 2013 | April 7, 2014 |
| 186.5.138.40 | Oct. 30, 2013 | Jan. 13, 2014 |
| 23.229.114.136 | April 14, 2014 | April 14, 2014 |
| 185.12.44.52 | April 14, 2014 | July 14, 2014 |
| 23.229.114.177 | April 14, 2014 | July 14, 2014 |
Success!!!!
Go from one TLS Cert, one IP, and one Domain
Get 6 IPs and Three Domains using same registration info
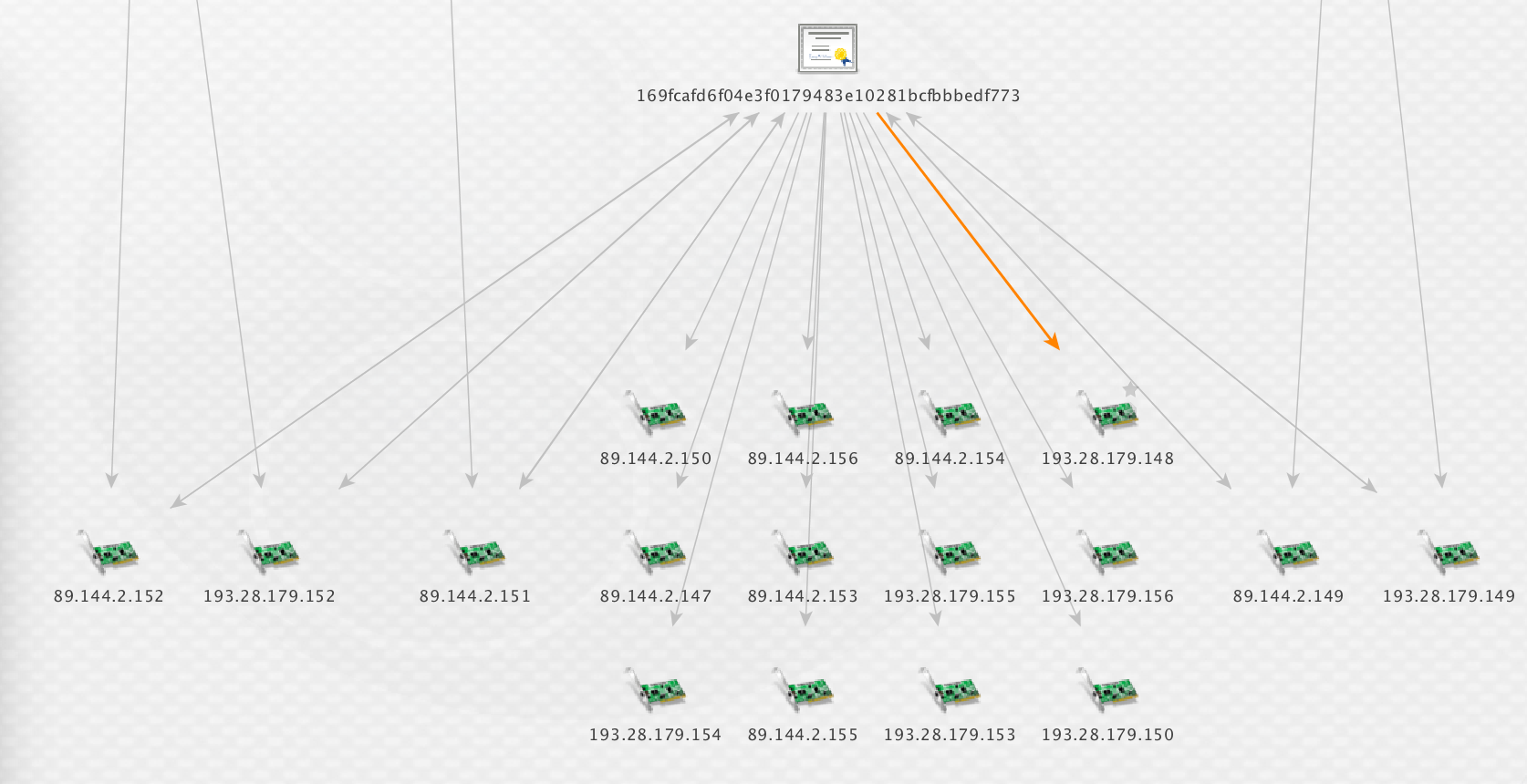
Palo Alto - Lotus Blossom

Great write up on targeting of Hong Kong, Taiwan, Vietnam, the Philippines, and Indonesia and the use of the Elise trojan
Provided csv of iocs on github
IP iocs
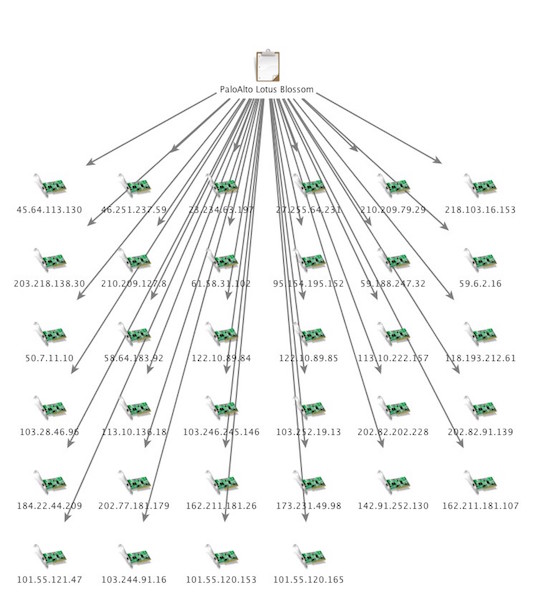
TLS Pivot
Hmmm several ip's all using the same TLS cert
Could there be more?
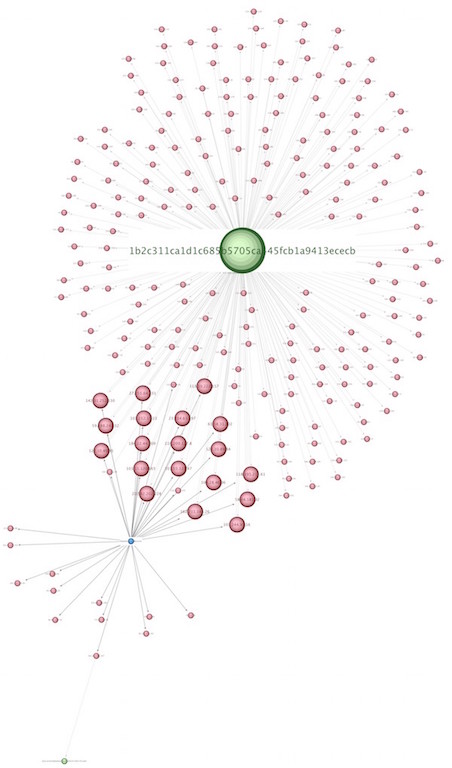
Yup! there is more - lots more
Almost 300 different ip addresses
Certificate Issuer: Eric-Office
Certificate Subject: Eric-Office
Validity Dates: 2012-02-13 - 2022-02-10
Sonar dates
First seen 2013-10-30
Last seen 2016-04-18
Still very active today
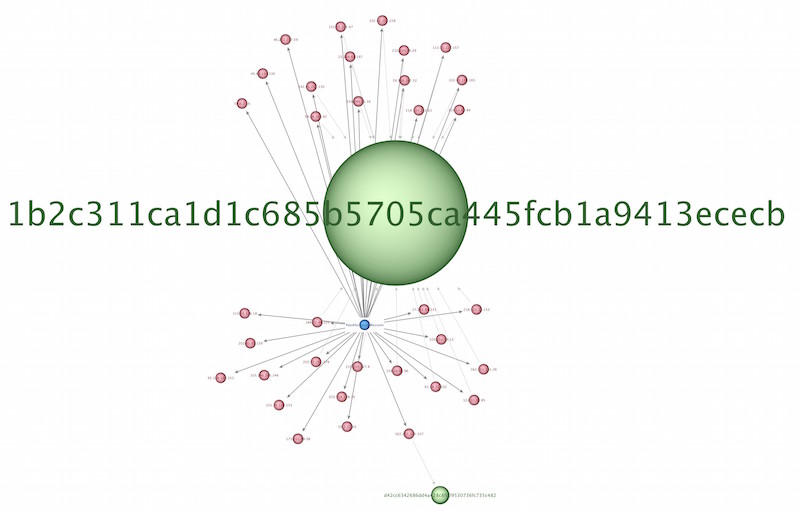
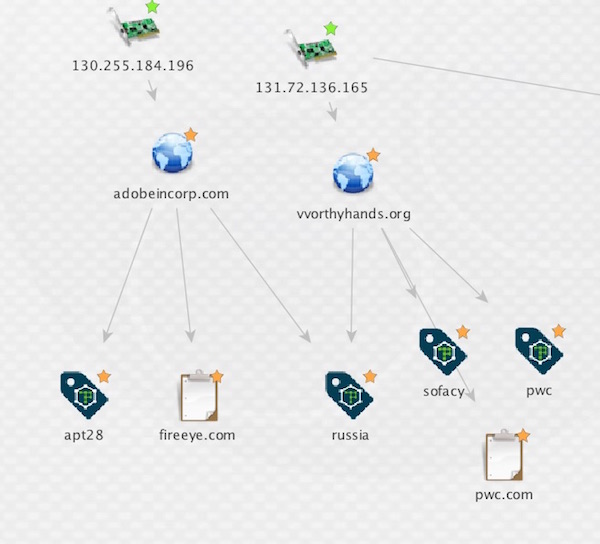
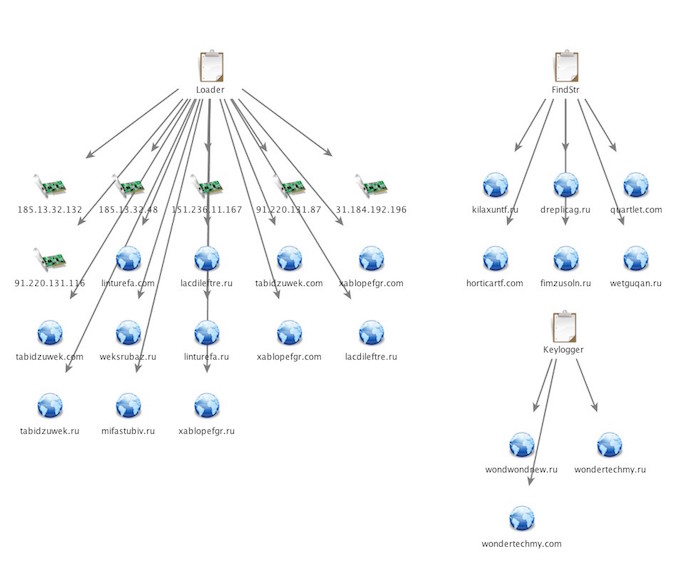
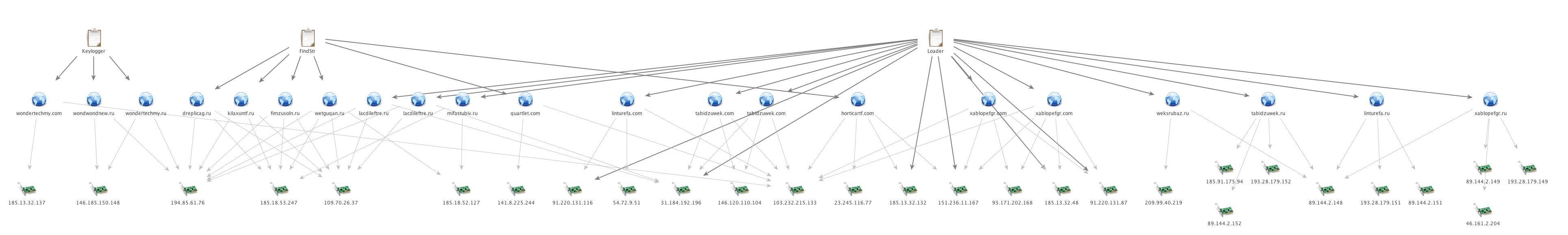
APT 28/Sofacy - X Tunnel

Initial IOC
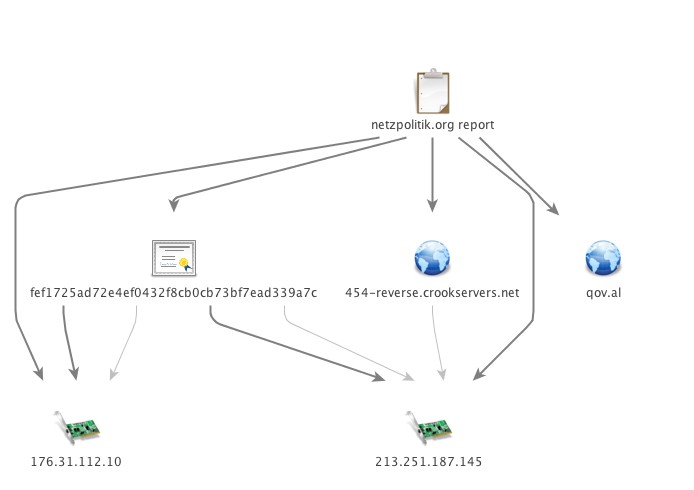
Passive DNS pivot
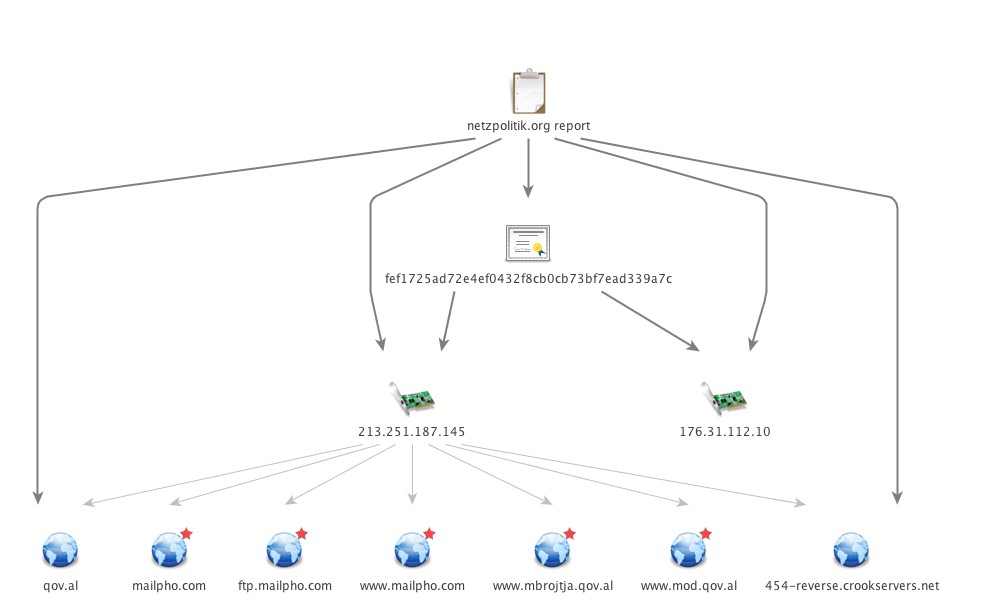
TLS Certificate pivot on initial IP's
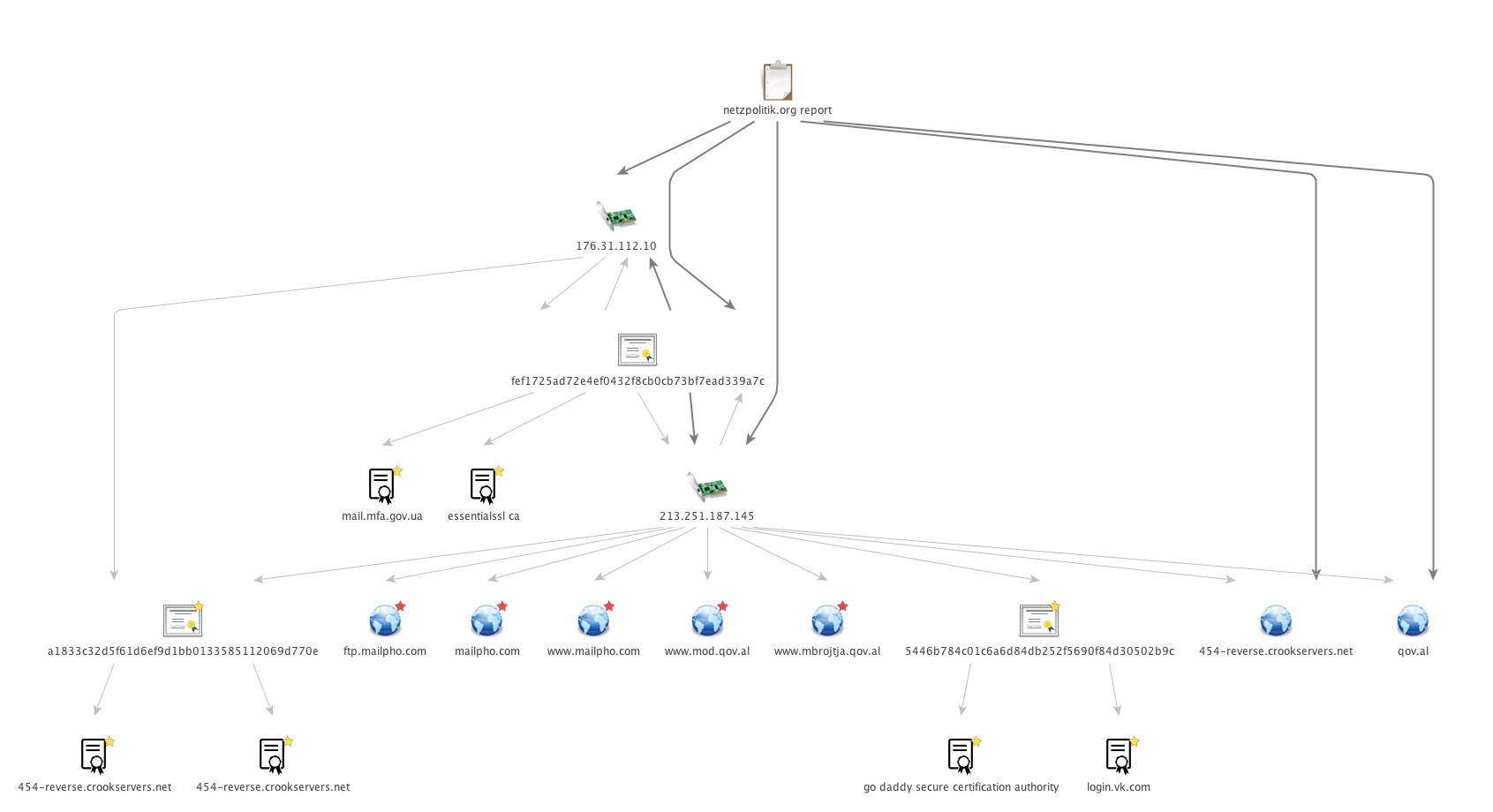
Pivot on new TLS certificates
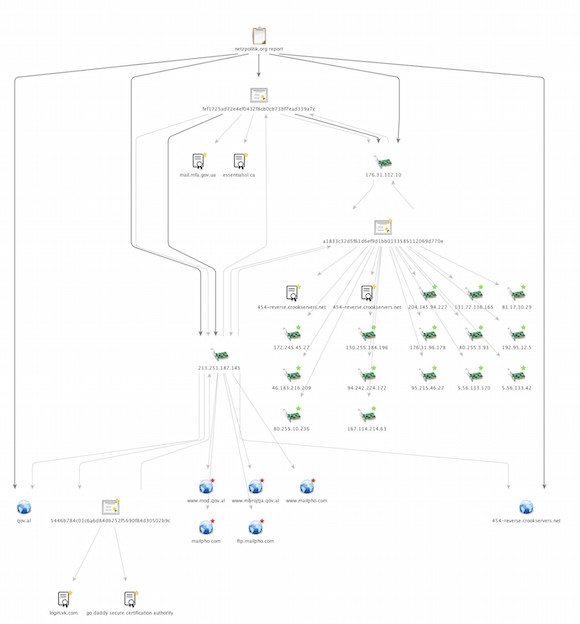
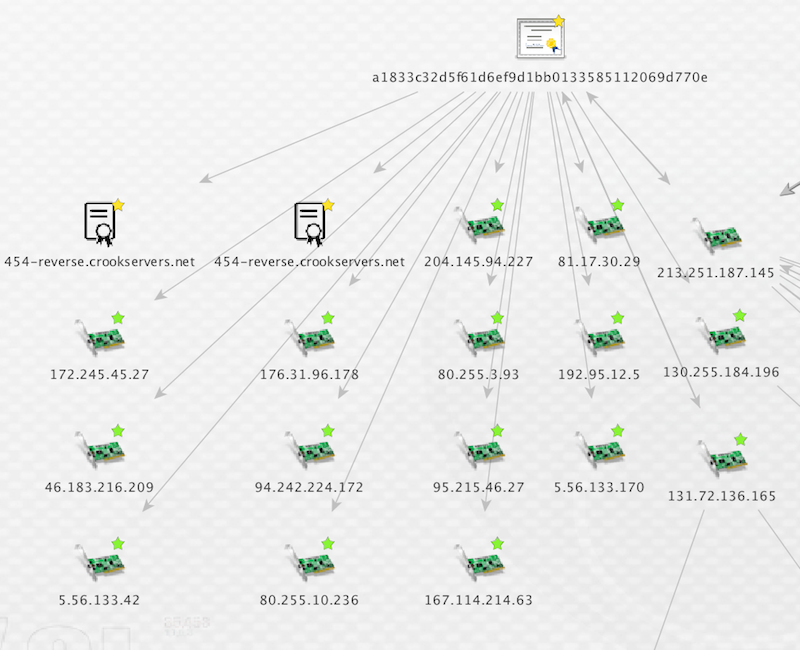
TLS pivot on new ip addreses
One interesting new certificate found
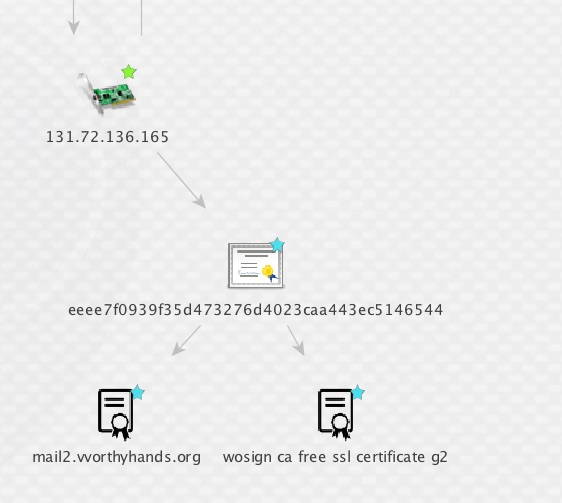
Passive DNS pivot on new ip addresses
Two interesting domains and osint reports
Initial report 2 domains, 2 IPs, 1 TLS Cert
Tradtional pivots reveal 5 interesting domains
Now have 17 IPs, 5 domains, 4 TLS certs
Additional linkages via OSINT reporting
Additional linkages via OSINT reporting
PoSeidon - Point of Sale

Initial IOCs
Passive DNS on domains
Pivot on TLS certificates found on IPs
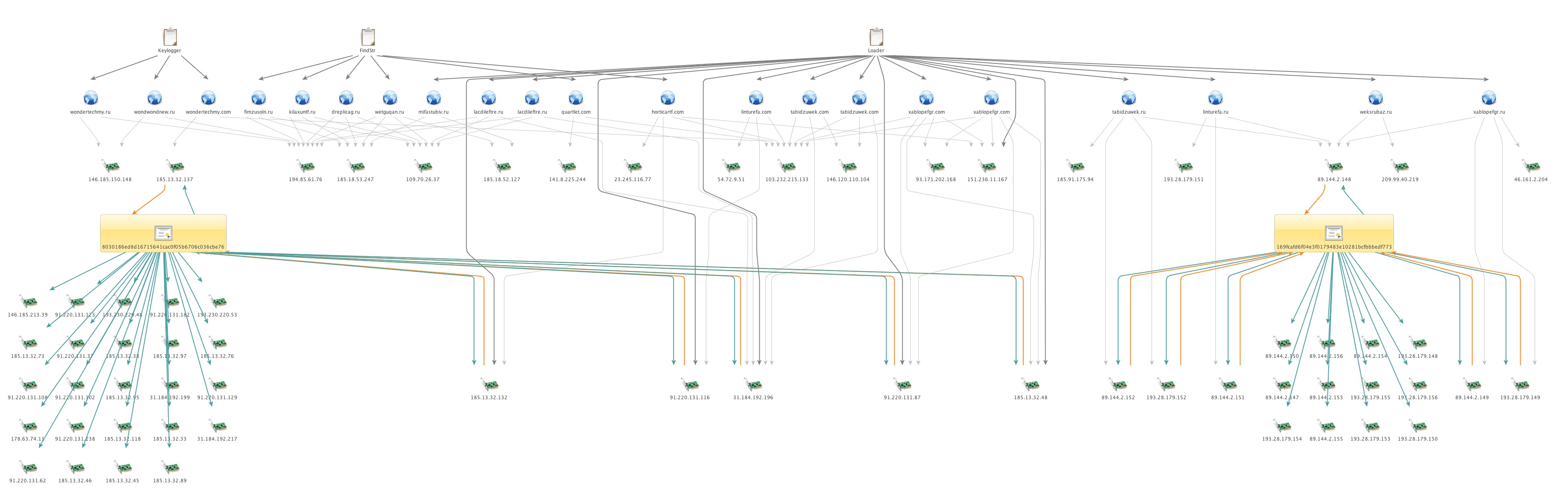
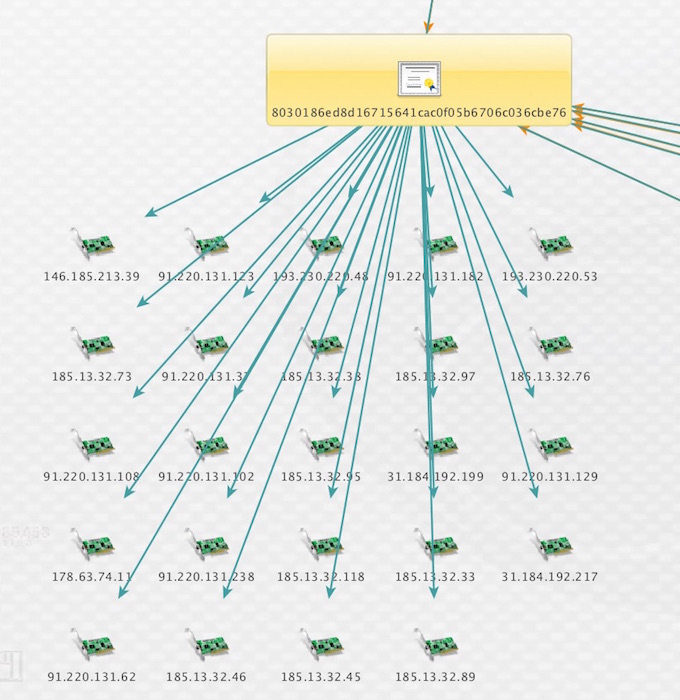
Start with 21 domains, 6 ip addresses
Basic pdns pivot adds 22 new ip addresses
2 new TLS certificates
36 new ip addresses using those TLS certificates
Much more to dig into
More pivots to be done but due to time constraints I will stop here and leave this as an exercise for you to try.
Thank you
A quick thank you to the people below for their help/support on this presentation.
- Ben Koehl
- Scott Roberts
- James Elliott
- Brandon Dixon and the team at PassiveTotal